Encrypted Traffic Analysis
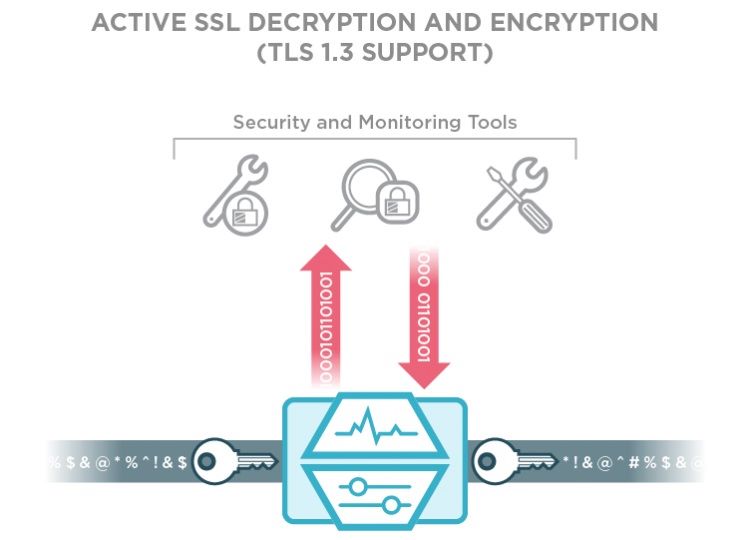
Nowadays, a major part of internet traffic is encrypted and attackers know that very well. Therefore botnet command & control communication and malware activities often hide within encrypted traffic. If your Windows 10 laptop suddenly starts communicating using a deprecated encryption algorithm in the SSL layer, you can be sure that such a device is compromised. What if your users communicate to servers with untrusted certificates? What is your current level of visibility into SSL/TLS traffic?
Let's explore how Flowmon deals with visibility into SSL/TLS protocols. Without the need to breach user privacy you can report on various characteristics of encrypted traffic, including protocol version, encryption algorithm, cipher suite or certificate details. Moreover, Flowmon supports JA3 fingerprint, designed to recognize malicious clients in the network based on their overall SSL/TLS characteristics.
Cryptographic assessment or compliance is when we audit our encryption stack to look for outdated protocols still in use, inadequate key lengths and expired certificates.
Use Case 1: TLS protocol version
Which TLS versions are out there in the wild? SSL Pulse provides an excellent dashboard updated every month with statistics about SSL/TLS versions, key lengths, cybersuites and vulnerabilities. With Flowmon it's easy to inspect the use of outdated TLS versions in your network. Take a look at this screenshot from Flowmon Monitoring Center:

Looks like there is a lot of traffic still using TLS 1.0. We can dig deeper and find out which local services / applications need to be upgraded:

Use Case 2: Public key length and algorithm
Weak short keys and outdated algorithms are a serious security risk. Insufficient key length makes it easier for an attacker to perform brute force decryption. Outdated algorithms suffer from vulnerabilities malicious actors can exploit to break in (think Heartbleed). Let's inspect public key lengths and algorithms in our network with Flowmon:

As we can see most of the encrypted traffic is using RSA with 2048-bit length, followed by ECC with 256-bit length (which is a rough equivalent to RSA 2048-bit) and followed by RSA with 4096-bit keys. This is good news, since it's recommended to use 2048-bit keys for RSA. However, there is still a small amount of traffic with only 1024-bit RSA keys. We can use filters with Flowmon to focus only on this traffic.
Further on, we could find the usage of short TLS keys in our network and we can take action to set it right. Flowmon enables you to set an alert any time a weak key is detected in your network and optionally send an email.
Use Case 3: Certificate checkup
While checking for expired certificates is an obvious step, we might also want to check for soon-to-be-expired certificates to prepare in advance. Furthermore, monitoring certificates and their usage in development, testing and production environments is a way to protect against and identify leaking private keys and other sensitive information. With Flowmon, we can look for certificates that will expire between today and by the end of the year by using a filter.
Summary
Companies risk serious consequences when ignoring encrypted traffic. Malware campaigns are increasingly taking advantage of encryption to hide. Flowmon enables regular cryptographic assessment to check for compliance with the latest security standards. Review the validity of certificates, pinpoint suspicious clients and much more, all without the need to breach user privacy with Flowmon. Set alerts to notify you whenever TLS parameters violate your internal policy.
And how will you leverage the new TLS capabilities?